Scattered Spider Is Back—and It’s Inside Your Slack
By David V. | 2/28/2026
The hacker group known as Scattered Spider (also tracked as UNC3944 and Okta Tempest) has moved well beyond phishing emails and SIM swapping.
They’re now infiltrating Slack channels.
Joining Microsoft Teams environments.
Spoofing HR onboarding workflows.
Even sitting in on live security calls.
This isn’t just hacking.
It’s impersonation, infiltration, and surveillance from inside your own collaboration tools.
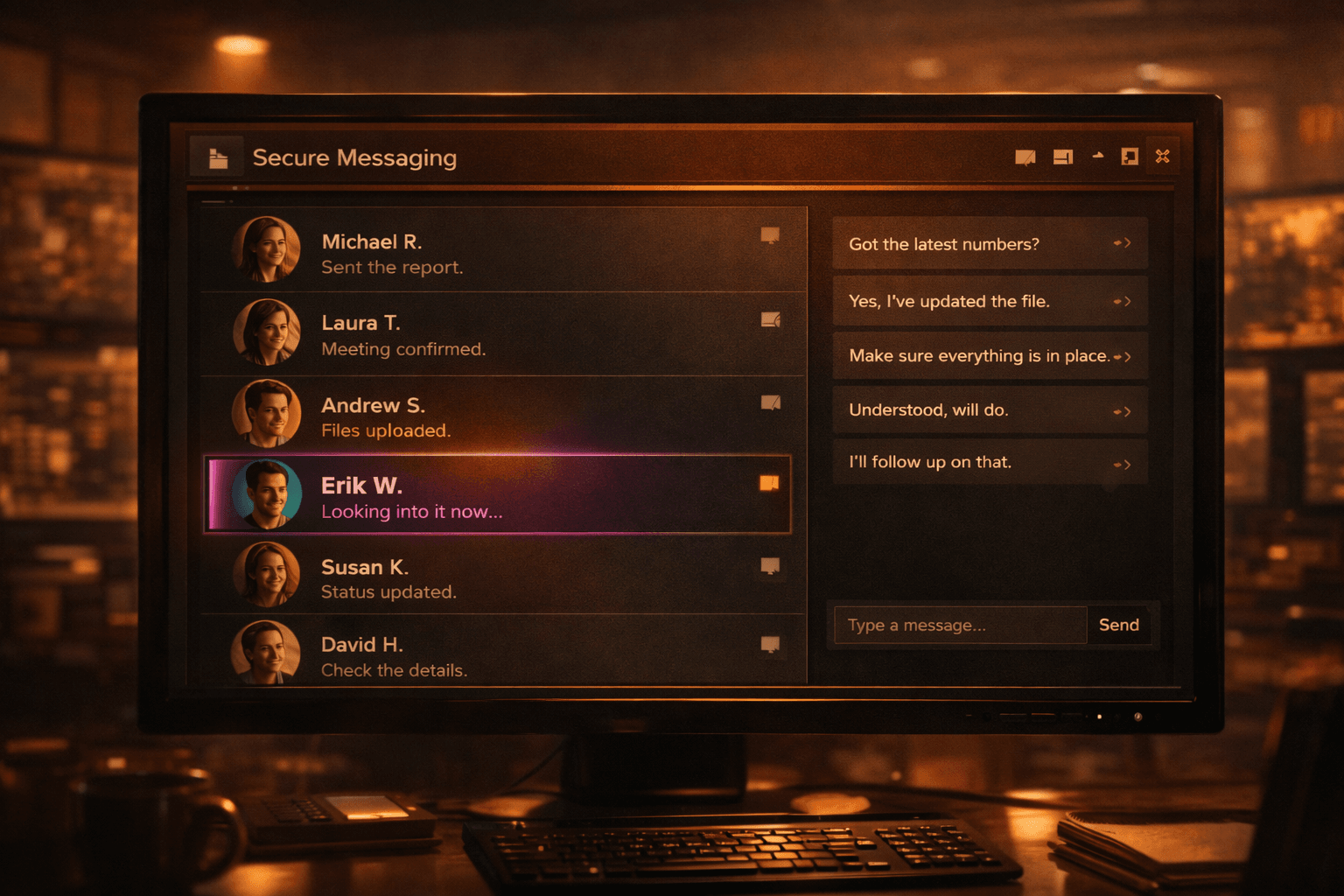
What’s New: Slack, Teams, Onboarding, and Calls
Recent joint advisories from the FBI, CISA, and international partners outline a significant escalation in tactics.¹²³
Scattered Spider is now:
Breaking into Slack and Microsoft Teams to read internal conversations, harvest session tokens, and impersonate users¹
Spoofing HR onboarding systems to pose as new hires and request legitimate access
Using help desk impersonation to reset credentials and bypass MFA protections²
Eavesdropping on live incident response calls to adapt their techniques in real time³
They combine strong technical tradecraft with aggressive social engineering.
The result? Access that looks legitimate.
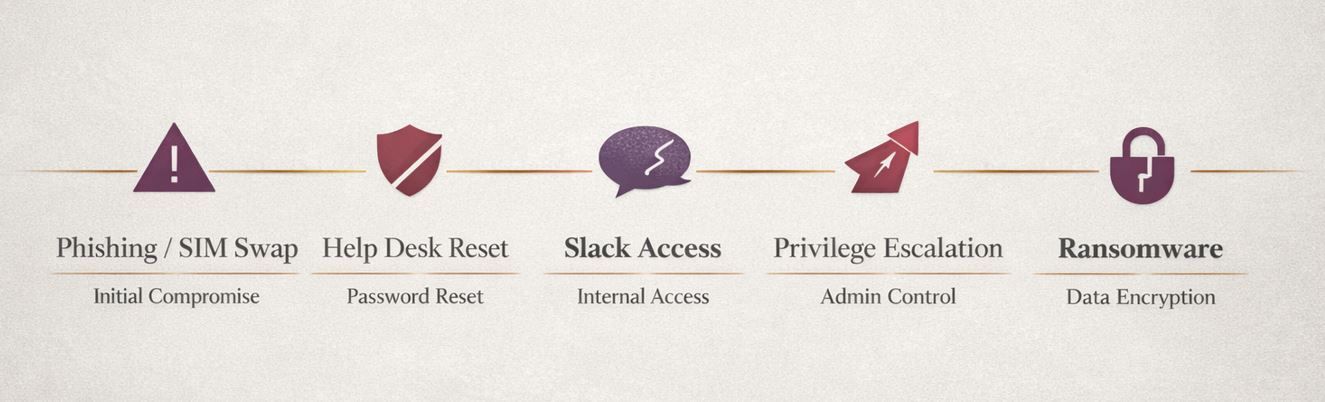
How the Infiltration Works
Unlike traditional ransomware groups that blast out phishing campaigns, Scattered Spider operates more like a patient insider.
A common pattern looks like this:
Gain initial access through phishing, SIM swapping, or help desk impersonation.
Harvest tokens or session credentials from chat platforms.
Escalate privileges quietly.
Observe internal workflows, security discussions, and access controls.
Deploy ransomware once positioned for maximum impact.
Because they infiltrate collaboration platforms, they can:
Study how your team communicates
Learn your incident response process
Identify high-value targets internally
Blend into routine conversations
This is reconnaissance from the inside.
Real-World Damage
Scattered Spider has been linked to attacks impacting:
Marks & Spencer, Harrods, and Co-op (UK) — using internal IT impersonation to reset staff credentials⁴
Major U.S. firms in telecom, insurance, and airlines — where infiltration campaigns led to ransomware deployment⁵
The group is frequently associated with ALPHV/BlackCat ransomware operations.
The pattern is consistent:
Access first.
Persistence second.
Encryption last.
Why This Is Different
Most organizations defend against external attackers.
Scattered Spider looks internal.
They don’t just steal passwords. They:
Join your meetings
Read your chats
Impersonate your employees
Monitor your defenses
If your security strategy assumes attackers stay outside the perimeter, you’re operating on outdated assumptions.
The collaboration layer has become an attack surface.
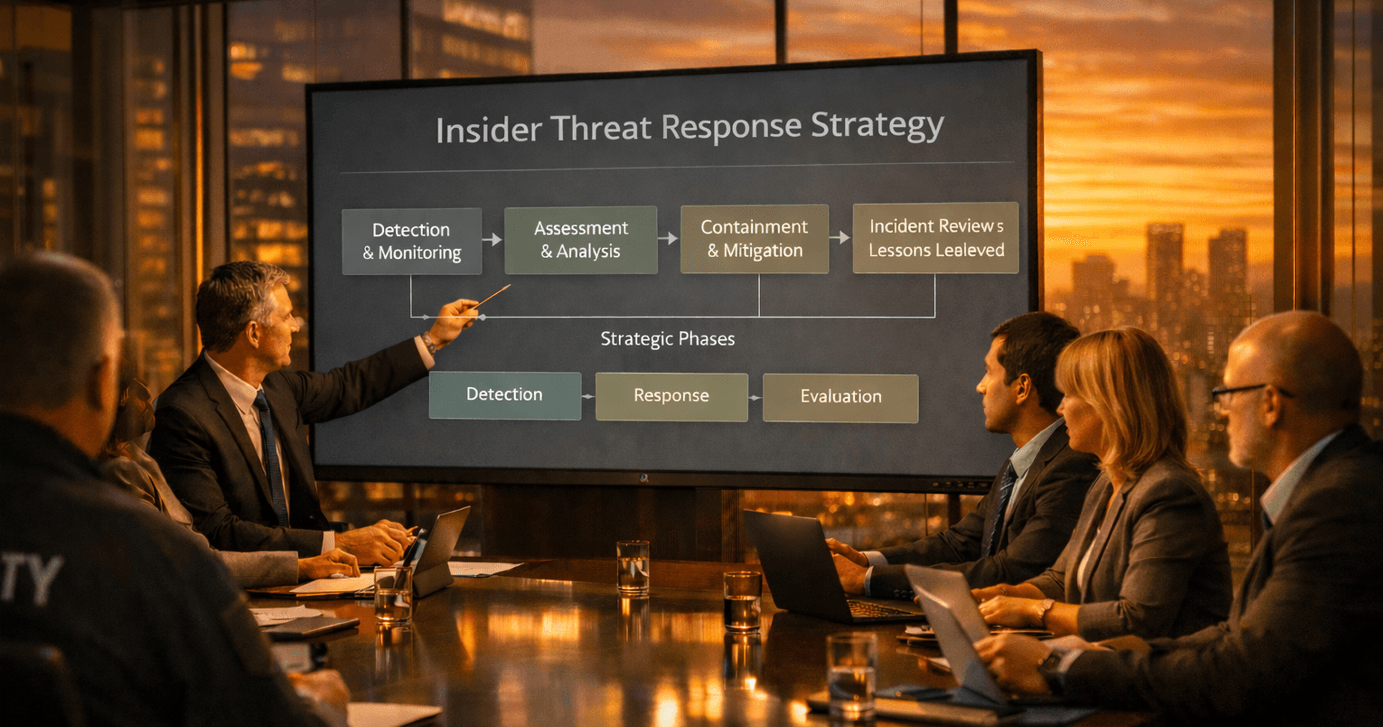
How to Stay Ahead
Defending against insider-style infiltration requires more than endpoint protection.
Start here:
Use phishing-resistant MFA (hardware tokens or passkeys instead of push-only authentication)
Restrict token sharing and session reuse in chat platforms
Manually verify all new onboarding access requests
Set alerts for newly created Slack or Teams accounts
Monitor for unusual remote access or “shadow IT” logins
Run tabletop exercises that simulate insider presence during an incident
Preparation must assume that attackers may already be in your communication channels.
Final Thoughts
Scattered Spider is redefining what it means to be “inside the network.”
They’re not just stealing credentials.
They’re joining your calls.
Reading your messages.
Learning your response plan.
If you’re not preparing your team for threats that look exactly like your coworkers, you’re already behind.
Identity and collaboration security aren’t optional anymore. They’re front-line defenses.
Key Terms
Push-Bombing – Flooding a user with MFA requests until one is approved
SIM Swapping – Hijacking a phone number to intercept authentication codes
Shadow IT – Systems or accounts used without formal IT approval
Insider Reconnaissance – Learning defense strategies from inside the environment
Token Theft – Stealing session credentials to bypass login controls
📚 Sources
- The Scattered Spider group is infiltrating Slack and Microsoft Teams to target vulnerable employees. ITPro, July 30, 2025.
- FBI, CISA warn of more Scattered Spider attacks to come. TechRadar, July 30, 2025.
- Scattered Spider tactics continue to evolve, warn cyber cops. ComputerWeekly, July 30, 2025.
- Scattered Spider service desk attacks: How to defend your organization. SpecopsSoft, May 7, 2025 (updated July 11).
- A Group of Young Cybercriminals Poses the ‘Most Imminent Threat’ of Cyberattacks Right Now. Wired, July 2, 2025.