
Hackers Are Now Threatening People—Not Just Systems
By David V. | 2/28/2026
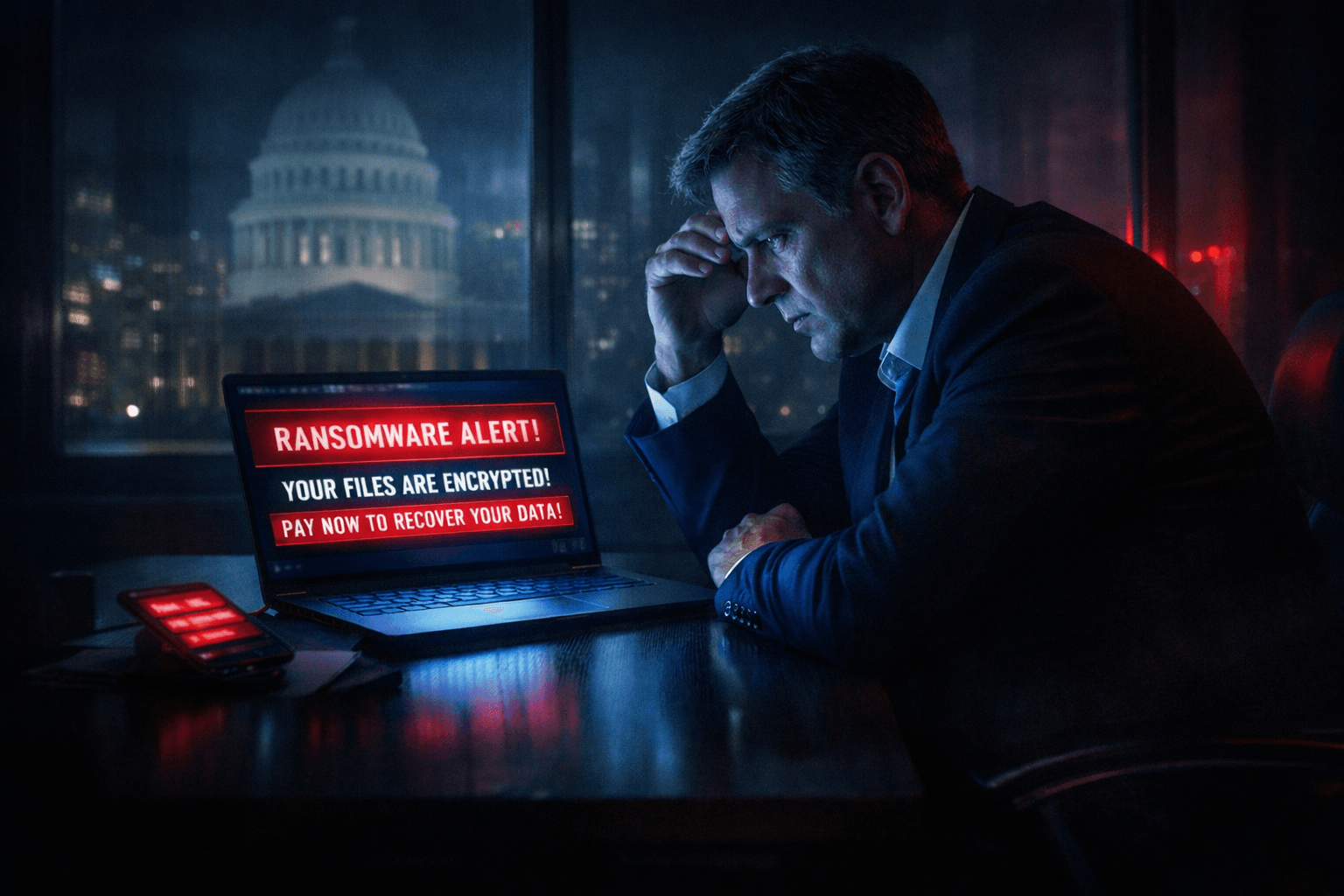
Cybercriminals have crossed a line.
Ransomware gangs used to stop at encrypting files. Then they started leaking data. Now they’re threatening executives, families, and even reporting victims to government regulators if the ransom isn’t paid.
This is a different level of pressure.
What’s New in 2025
According to new reporting highlighted this year, the ransomware landscape has shifted in a way that goes beyond technical compromise¹².
40% of ransomware incidents now involve physical threats
In the United States, that number climbs to 46%
47–58% of incidents include threats of regulatory complaints, often tied to SEC disclosure rules
55% of victims report multiple ransom demands
Attackers aren’t just demanding money. They’re filing complaints, doxxing executives, and manufacturing reputational crises to increase leverage.
This is extortion layered with psychological warfare.
How the Threat Works
Modern ransomware groups are blending real-world intimidation with legal manipulation.
Here’s how the playbook typically unfolds:
Mining data broker sites and LinkedIn for executive contact details
Sending threats directly to leadership or family members
Threatening to leak home addresses or personal information
Filing SEC complaints before the victim company can disclose the breach
Contacting journalists or leaking selective information to force public pressure
The objective isn’t just encryption.
It’s panic.
Attackers want leadership distracted, fearful, and pressured from multiple angles at once.
Quick Threat Breakdown
Tactic | Prevalence (2025) |
|---|---|
Physical threats to executives | 40% (U.S.: 46%) |
Regulatory complaint threats | 47–58% |
Multiple ransom payments | 55% |
The escalation is clear: attackers are stacking pressure tactics instead of relying on one.
How to Defend Against This Level of Pressure
These aren’t just IT incidents anymore. They’re legal, reputational, and personal threats.
Defense has to reflect that reality.
Scrub executive information from data broker sites (use removal services where appropriate)
Build a crisis communications plan that includes SEC, media, and legal response
Set up monitoring for impersonation attempts and fake breach reports
Train executives to handle social engineering and extortion scenarios
Include legal and PR teams in tabletop incident response exercises
Develop a response plan if attackers contact customers, board members, or journalists
If your incident response plan only lives in IT, it’s incomplete.

Final Thoughts
Ransomware isn’t just about your files anymore.
It’s about your leadership.
It’s about your reputation.
It’s about forcing emotional decisions under extreme pressure.
If you secure your network but ignore your people, you’re not prepared for where this threat has gone.
This is no longer a purely technical battle. It’s organizational resilience under stress.
Key Terms
Physical Threats – Intimidation directed at individuals to enforce ransom payment
Regulatory Sabotage – Filing real or fraudulent complaints with agencies such as the SEC
Doxxing – Publishing private personal information online
Data Brokers – Companies that collect and sell personal information
Crisis Communications – Structured emergency messaging for regulators, media, and stakeholders
📚 Sources
- Ransomware gangs are now expanding to physical threats in the real world. TechRadar, August 1, 2025.
- Companies pay multiple ransoms as attackers step up threat levels. BetaNews, July 31, 2025.